‘We need to be alert in terms of detecting suspects’ hidden messages’
Hidden messages in seemingly innocent videos, photos, audio or text. Criminals can use these messages to notify others in which container they have concealed drugs or display child sexual abuse material on a public platform. The hidden messages are hard to spot with the naked eye. The Netherlands Forensic Institute (NFI) is participating in the European UNCOVER project, which entails law enforcement agencies working with universities and businesses to develop tools to detect and read hidden messages in videos and images.

The art and science of hidden messages is called steganography, explains Meike Kombrink, who is working on steganalysis (hidden message detection) at the NFI. ‘It’s an art form because it’s creative, but it’s a science because you need to know how to hide the message in digital images or videos. You need to know how it works.’ Criminals and terrorists can use steganography to hide information and communicate with one another. ‘Cryptography and steganography are closely related. Cryptography involves concealing the content of the message, and steganography involves concealing the existence of the message.’
9/11 attacks
Al-Qaeda supposedly used steganography to plan the 9/11 attacks, as revealed by a scientific publication (Dalal and Juneja, 2021). The paper also mentions that Russian agents used steganography in 2010 to send secret messages to Moscow. The method was discovered by the FBI. Child sexual abuse material was concealed in seemingly innocent images in the Shadowz Brotherhood case. International scientists are warning that steganography has been rising in popularity since law enforcement agencies demonstrated that they can crack encryption using EncroChat (O'Rourke, 2020).
Examples in the Netherlands
Several criminal cases in the Netherlands have involved suspects using steganography. In those cases, the NFI was able to read the messages. ‘Steganography’ was used in an extortion case back in 2003, for instance. The suspect asked to receive hidden bank details via an image posted on a certain website, otherwise the extortionist would follow through on threats. ‘We suspect that it’s being used,’ says Kombrink. ‘You can’t spot it with the naked eye. It’s probably a lot more common than we’re seeing. That is why we keep raising awareness and drawing law enforcement agencies’ attention to it.’
Adjusting the colour intensity of images
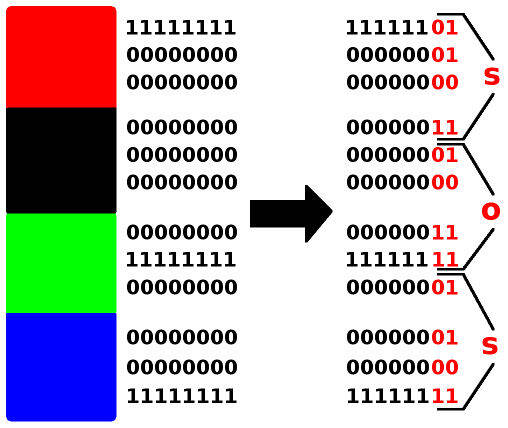
An object containing a hidden message is called a cover. There are three commonly used ways of concealing messages in images, each of which also has several variations. The first way is to modify the binary values of the colours in images. This involves adjusting the colour intensity of a pixel, for example. ‘You add a tiny drop of red, as it were, to the colour code. You can’t see the difference just by looking at the photo. You can sometimes spot it when looking at the binary values. Again, the modified values can indicate the presence of a hidden text.’
Compression
Another method of concealing messages is by means of transformation, a different way of displaying the image. One example is to compress the file, i.e. reduce it in size in order to save it. ‘That involves creating a kind of summary of the image, as it were,’ explains Kombrink. There are various ways of summarising an image. The most important numbers for the image end up in the summary. If you know where they are, then you can conceal a message there. ‘You won’t see the message in the full-sized image. It only becomes visible once you have made a summary of the image and know where in the summary the message will be hidden.’
Producing a cover yourself
The third way is to use AI to generate images, audio or text concealing a message. Ordinarily, you will have an original image in which a message is concealed by making some adjustments. ‘Which means you need to have a good idea as to where you can conceal the message without changing the way the image looks. On the edges of the objects, for instance.’ You do not need such knowledge for the third method. ‘Here, you don’t have an original; the neural network itself produces an image with the hidden message pre-concealed.’
Detecting steganography
The NFI is currently investing in automated systems to detect steganography in conjunction with European partners. The NFI is researching whether neural networks are effective at detecting concealed messages. In terms of their structure, neural networks were inspired by the human brain. The models learn in a similar way to human learning, i.e. through looking at lots of examples.
S A student from Eindhoven University of Technology recently studied whether neural networks are capable of discovering concealed messages in video files (video steganalysis). The student Mart Keizer, was commissioned to do so by us in the context of an internship. For the purposes of the study, the student produced a large data set containing videos that did or did not contain concealed messages. Giving the neural network an ample quantity of videos and informing it as to whether or not they contained a concealed message enabled the network to discover a particular pattern for itself. This allows it to detect wether a video contains a concealed message. Once the network has been ‘trained’, it can be used to ascertain whether or not there is a concealed message in a video file. Further research is needed, but the initial results were promising, with the detection rate for two researched types of steganography being 99.96%.
Message reading tool
It is not enough to just develop detection tools, says Kombrink. ‘Steganography in itself isn’t a criminal offence at present. You could also conceal perfectly innocent messages. Hence, you need to know the content in order to identify a less innocent message. And so I’m also keen to train neural networks to automatically read messages.’ Kombrink suspects that steganography is not currently being used in straightforward crime. ‘You still always need to communicate the method that is used to hide the message and thus is needed to extract the message. It is therefore more likely to be used for high-impact crimes.’ Once the tool is ready, Kombrink thinks it would be a good idea to add it to the Hansken digital search engine, which can be used to examine vast quantities of digital data in criminal cases. ‘It’ll be interesting to see. Only once the tool is up and running will we find out on what kind of scale steganography is being used in the Netherlands. Until then, we need to stay alert when performing manual searches.’
AI4forensics
Kombrink’s PhD project is part of the ICAI AI4forensics lab being set up with the University of Amsterdam and the NFI under the supervision of Prof. Marcel Worring and Prof. Zeno Geradts.