European project EXFILES hacks the latest cryptophones
Hacking cryptophones. That is what the European project EXFILES is all about. Not only various law enforcement agencies, but also companies are working together on the project to develop new methods and techniques to gain access to the latest cryptophones. The Netherlands Forensic Institute (NFI) is one of the participants of the project, which ends this summer. “EXFILES has made an important contribution towards gaining access to hundreds of mobile phones, mostly in the context of investigations into serious organised crime for Dutch investigation agencies,” said head of the NFI’s Digital and Biometrical Traces division Erwin van Eijk: “At the European level, many times over.”
Whilst obtaining access to messages on cryptophones has become more relevant in recent years, it has also become more complicated. “These days mobile phones have multiple layers of encryption and the phones are modified at the software level,” van Eijk said: “That makes it necessary for forensic digital examiners to collaborate within Europe. Developments happen so fast that we have to join forces.” EXFILES began in July 2020 and will end this month.
Serious organised crime
The knowledge that the NFI acquired during the project could immediately be applied to criminal cases. Martijn Egberts, National Public Prosecutor for Digital Investigations finds it important that experts share the knowledge with each other in regards to accessing mobile phones: “That way, the police and the Public Prosecution Service can still use the decrypted information originating from these kinds of seized cryptophones as evidence in criminal cases.” The messages play a major role in a great many investigations into organised crime. “A large proportion of the messages come from cryptophones which the NFI succeeded in hacking. In many cases, it concerns evidence that the judicial authorities were unable to collect in any other manner”, said Egberts.
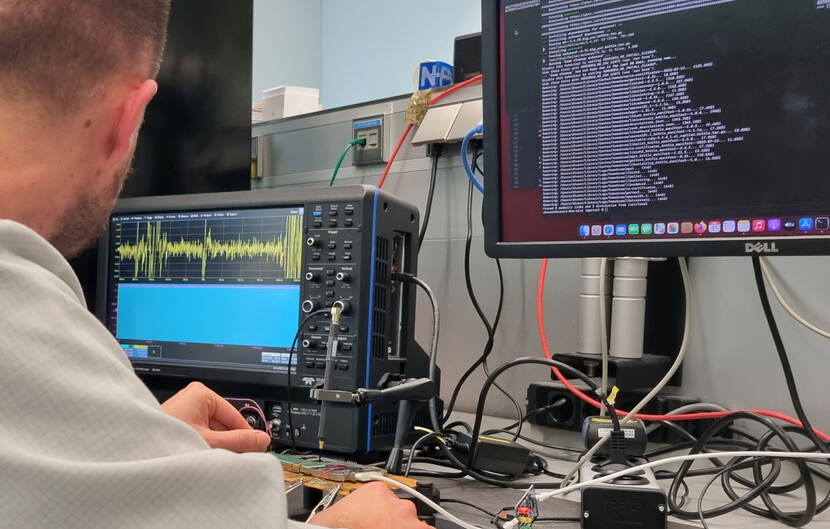
Combination of hardware and software
In order to obtain readable data from mobile phones, the examiners must always search for the weak links. “At first, it was possible to retrieve information directly from the hardware (chips). Next the information was encrypted using keys that were saved on yet other chips, combined with the passwords created by the users themselves,” said van Eijk: “Nowadays a combination of knowledge about hardware and software is needed to obtain access to encryption keys. In addition, knowledge of cryptography is required in order to search for passwords efficiently. For example, the examiner must first edit the chip to subsequently access decrypted user information via software. People often specialise in either hardware or software techniques, said van Eijk. “Within the EXFILES project, we literally bring people in various specialist areas together to develop new solutions. And it was precisely that which resulted in breakthroughs.”
Looking ahead
In the EXFILES project, the forensic researchers and law enforcement agencies together prioritise which knowledge and expertise, with regard to which kinds of cryptophones, must be developed first and for which cryptophones they can best share methods of access. In so doing, the investigators look at sales figures, for example, but also trends they identify among suspect or criminal groups. Technicians from all over Europe then come up with solutions together. As a result, the methods that enable access to these kinds of cryptophones have usually already reached an advanced stage once the police seizes them. In this way, the NFI is ready for the forensic demands of tomorrow. “It doesn’t matter to me whether it concerns incriminating material or not. Getting access to information helps with establishing the truth in the court of law,” said van Eijk. “If the technique works and we gain access, then we will deem the project a success.”
In October, the European Commission will evaluate the project and the decision will be made as to whether there will be a follow-up.